Recently, I've *allegedly* received some documents on torrent clients on my network. Of course, I wholeheartedly respect copyright laws and do my utmost to ensure that files on my systems are 100% legal. Regardless, I thought creating an offsite file download/share server might be an exciting project.
I already had a VPS I was renting from a VPS provider, so I spun up another one with them. Relatively low specs, 4 CPUs, 4GB RAM, but it has unlimited network usage which is good for my purposes. I went with the most recent version of Ubuntu, but any OS would work with this.
To start off, I had an idea for a setup that used a management IP that I could access to download files and communicate with the torrent client, and a download IP that ran a VPN at all times and was only used for downloading files. Luckily enough, my VPS provider had options for adding extra IPv4 addresses to the server, so I bought an extra address and got that working. OpenVPN also has an option to bind to a specific address, so I was banking on attaching that to the secondary IP and then using the primary IP for management. Unfortunately, both IPs were routing off of the same NIC, so while OpenVPN was biding to the correct IP, it was still affecting both addresses.
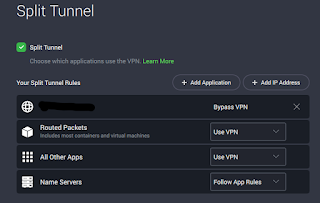
This meant that I couldn't access the server using the management IP I was setting up, so I had to find a different VPN solution. I ended up going with split tunneling, which isn't necessarily ideal, but for my purpose should be fine. My VPN provider has a Linux application that works fairly well and supports split tunneling natively, so I went with that over other options. I was also able to mess with some of the VPN settings to make it slightly more secure. I set it up with my personal IP whitelisted so that traffic from my home network and the remote server wasn't captured by the VPN and I would be able to access my management portals.
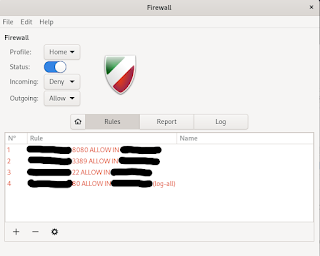
Next, I implemented a firewall to prevent other people from accessing the server. I'm a Windows guy and iptables can be a little frustrating for me, so I used gufw instead. It's essentially a GUI for iptables. It's a little more restrictive than CLI iptables, but again, for my purposes, it works well enough. Basically, I created deny all rules for incoming traffic and whitelisted my IP for web communication and SSH/RDP. I opened RDP as well as SSH because I've been on an RDP kick recently, setting it up on all of my non-interenet-facing servers. Xorg can be a little wonky, but it's been working well so far.
Comcast, if you see this, you know I was joking about those letters, right? :)





Comments
Post a Comment